CYBERSECURITY + IT
Build a Cybersecurity and IT Program that Prepares Students for the Real-World
Browse by Subject
Virtual Lab Environments
Hands-on virtual labs provide immersive mock IT infrastructures where students can test their skills in realistic security scenarios. Available as a standalone lab solution or bundled with our textbooks, Cloud Labs are an essential tool for mastering key course concepts through hands-on training. We also offer sandbox environments for programming students that are adaptable to meet your needs.
Quality & Current Content
Whether you’re teaching programming, information assurance, or IT security courses, we offer a suite of content covering the latest industry trends and tactics and written by today’s industry experts to prepare tomorrow’s information security and technology professionals. Our content is mapped to industry standards, including NICE, CSEC, CompTIA Security+, and more.
Instructor Resources
From lecture slides in PowerPoint format to sample syllabi to curriculum mapping, we make teaching cybersecurity, IT, and computer science courses easy with our robust instructor resources for classroom-based and online learning environments.
Just Published
Essentials of Computer Organization and Architecture presents computing systems as a series of layers, taking a bottom-up approach by starting with low-level hardware and progressing to higher-level software.
Learn More
Best Selling
A comprehensive overview of the concepts readers must know as they pursue careers in information systems security. Available with new Cybersecurity Cloud Labs.
Request Review Copy
Featured Cloud
Labs
The text helps students understand the difference between traditional database technology and the new directions created by big data, outlining motivation, fundamental concepts, technologies, and challenges associated with handling large datasets.
New Edition
Ethical Hacking: Techniques, Tools, and Countermeasures, Fourth Edition, covers the basic strategies and tools that prepare students to engage in proactive and aggressive cyber security activities, with an increased focus on Pen testing and Red Teams.
Learn More
Featured Blog
When it comes to cybersecurity, people are the weakest link—unless we educate them. Read on to learn how to combat cyber threats through great education and the right tools.
Learn More
Just Published
While technical skills are undoubtedly essential, cybersecurity instructors must recognize the growing need to equip students with a comprehensive understanding of the business side of cybersecurity.
Read Our TipsFeatured Webinar
Teaching Databases: Combining Databases Illuminated with Hands-On Cloud Labs
Recent Webinars:



Have a Look at Some of Our Market-Leading
Cybersecurity + IT Educational Resources
Your department or school doesn’t have to start from scratch. We have the tools and resources to build the right cybersecurity curriculum for your students, encourage hands-on learning, and empower instructors to deliver the best classroom experience.
Designed for in-person, online, or hybrid classrooms, Jones & Bartlett Learning’s turn-key cybersecurity curriculum solution combines print and digital textbooks with virtual machine lab exercises and comprehensive instructor resources to create an unmatched educational experience for instructors and students alike.

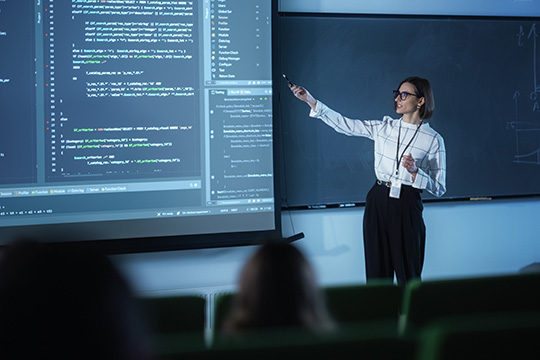
Colleges and companies are rapidly launching and scaling cybersecurity and information technology course offerings to meet the growing demand for qualified professionals. And yet, not every program is adequately preparing students to protect the valuable assets of organizations and individuals. Cybersecurity students need real-world experience and quality, current content to stay engaged in the classroom, drive learning outcomes, and hit the ground running after graduation.
The Information Systems Security & Assurance (ISSA) Series provides the Information Security and Technology professionals of tomorrow with practical and engaging academic content from today's industry experts. While we firmly believe the next generation of cybersecurity and IT education is hands-on and experiential, we also recognize that books are still essential learning resources in classrooms worldwide. The principal objective of our textbooks is to provide authoritative and durable content that serves as a strong knowledge foundation for students taking the first steps toward their future careers.


Our Cloud Labs provide fully immersive mock IT infrastructures with live virtual machines and real software, where students will learn and practice the foundational information security skills they need to excel in their future careers. Unlike simulations, these hands-on virtual labs reproduce the complex challenges of the real world without putting an institution's assets at risk. Available as a standalone lab solution or bundled with our textbooks, Cloud Labs are an essential tool for mastering key course concepts through hands-on training.


